The technological landscape in Latin America and the Caribbean for 2026 has shifted from a promise of development to a digital battlefield. With the rise of remote work, the explosive digitization of banking, and the rapid expansion of e-commerce across the region, the attack surface has grown exponentially. For a CFO in Santo Domingo, a CISO in San Juan, or an IT director in Kingston, the reality is stark: simply "having an antivirus" is no longer enough.
At V-Corp International, we have witnessed firsthand how threat actors are specifically targeting the Caribbean and Latin American markets. Why? Because they perceive a gap between digital ambition and defensive maturity. This article outlines the integrated security architecture we deploy for our clients—one that moves beyond point products into a cohesive ecosystem of resilience.
The regional threat context: why 2026 is different
Before selecting tools, one must understand the terrain. The threats facing LATAM and Caribbean enterprises in 2026 are characterized by three distinct trends:
| Threat Vector | Regional Impact | Industry at Highest Risk |
|---|---|---|
| AI-Generated Social Engineering | Deepfake audio calls to finance teams, synthetic identity fraud | Banking, Fintech |
| Supply Chain Compromise | Managed service providers breached, affecting downstream clients | Hospitality, Retail |
| Ransomware-as-a-Service | Double-extortion models targeting SMEs with limited backup maturity | Healthcare, Manufacturing |
| API Abuse & Bot Attacks | Credential stuffing against mobile banking apps, inventory scraping | E-commerce, Fintech |
The Caribbean faces an additional compounding factor: climatic resilience. A hurricane can physically destroy on-premise infrastructure just as effectively as a ransomware payload can logically destroy data. Any security strategy that ignores business continuity is incomplete.
"In 2026, cybersecurity in the Caribbean is not an IT issue. It is a business survival issue." — V-Corp International Security Architecture Team
Our approach at V-Corp International is to design ecosystems, not sell boxes. Below is the four-layer architecture we implement for regional enterprises.
Layer 1: The Perimeter — Consolidated Defense with Fortinet
The network edge remains the most vulnerable point of entry. For organizations managing distributed properties—whether a hotel chain across five islands or a bank with rural branches—the complexity of multiple consoles creates dangerous blind spots.
Fortinet's Security Fabric solves this through architectural consolidation. Rather than managing disparate firewalls, switches, and access points separately, Fortinet enables a single-pane-of-glass approach where every device shares threat intelligence in real time.
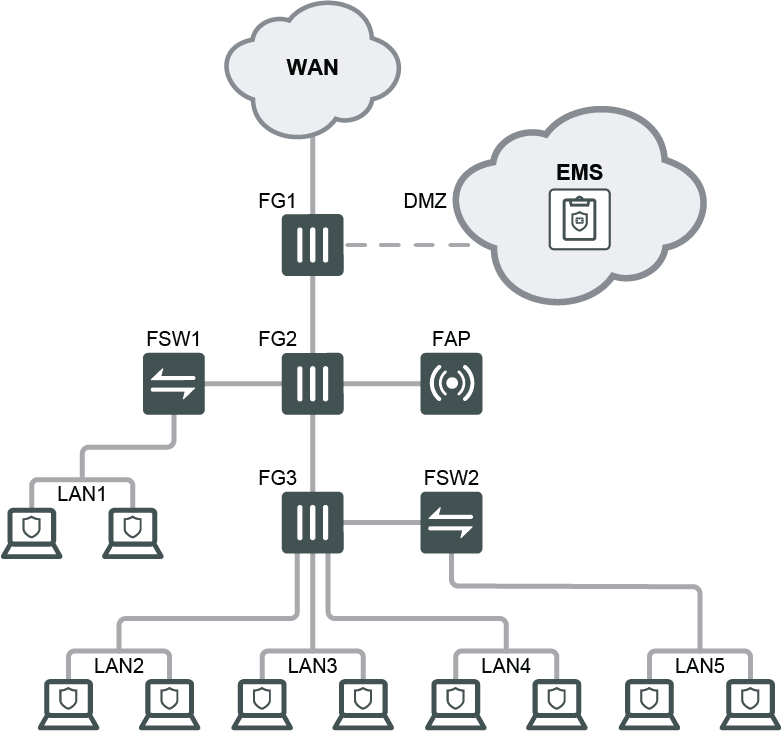
Why this matters for the Caribbean:
- SD-WAN integration allows a hotel in Barbados to maintain secure, optimized connectivity to its reservation systems even if the primary ISP fails during a storm.
- Zero Trust Network Access (ZTNA) ensures that remote employees—now the norm in regional back-office operations—never expose internal resources directly to the internet.
- FortiGuard AI updates threat signatures across the entire fabric within minutes, critical when new ransomware variants target Spanish and Portuguese-speaking enterprises.
For sectors like hospitality and tourism, where guest Wi-Fi networks represent both a service necessity and a security liability, Fortinet's ability to segment traffic (corporate vs. guest vs. IoT) without performance degradation is invaluable.
Layer 2: The Human Vector — Email Intelligence with Barracuda
If the perimeter is the gate, email is the key that most attackers try to steal. Despite years of awareness campaigns, Business Email Compromise (BEC) remains the highest-grossing cybercrime category globally, and Latin America is no exception.
Barracuda Email Protection deploys AI not as a buzzword, but as a behavioral engine. It learns the communication patterns of your executives, your vendors, and your finance team. When an attacker impersonates your CFO to request an urgent wire transfer, Barracuda detects anomalies that rule-based filters miss: subtle changes in writing cadence, unusual timing, or spoofed reply-to domains.
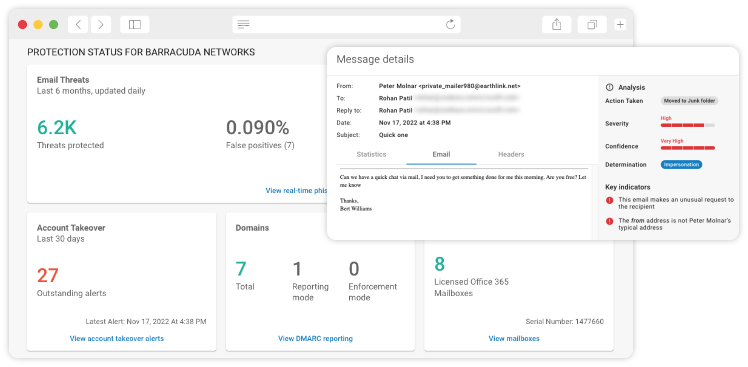
Critical capabilities for regional banks:
- Account Takeover Protection: Detects when a legitimate user account has been compromised and begins sending malicious emails internally.
- Conversation Hijacking Detection: Identifies when attackers insert themselves into existing email threads—an advanced technique increasingly common in BEC campaigns targeting Latin American trade finance.
- Automated Incident Response: Quarantines suspicious emails across the entire tenant within seconds, preventing the "patient zero" click.
In our deployments for financial institutions, we pair Barracuda with security awareness training, creating a human firewall that complements the technical one.
Layer 3: The Application Shield — Intelligent Protection with F5
For businesses whose revenue flows through web applications—Fintech platforms, e-commerce portals, and online banking interfaces—the application layer is where money changes hands and where attackers focus their most sophisticated efforts.
F5 Distributed Cloud Services provide protection that operates at the speed of business. It is not merely a Web Application Firewall (WAF); it is an intelligent traffic management and security platform that ensures legitimate users experience sub-second latency while malicious actors are stopped before they reach your origin servers.
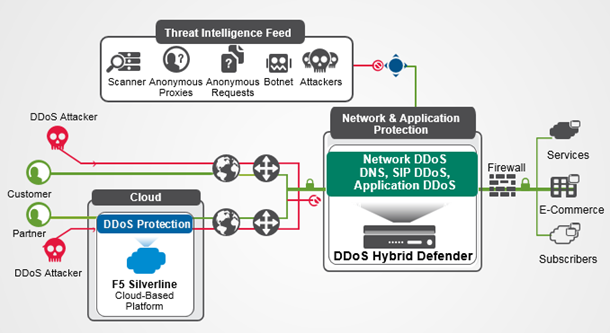
The F5 advantage in high-transaction environments:
- DDoS Mitigation: Absorbs volumetric attacks at the edge, preventing bandwidth saturation during peak retail or payroll periods.
- Bot Management: Distinguishes between legitimate automation (search engine crawlers, partner APIs) and malicious bots (credential stuffers, inventory hoarders) using behavioral biometrics.
- API Security: As open banking regulations expand across Latin America, F5 discovers and protects API endpoints that development teams may have inadvertently exposed.
For our e-commerce and Fintech clients, F5 represents the difference between a checkout process that converts and one that collapses under attack—or worse, leaks customer payment data.
Layer 4: The Nervous System — Observability with Elastic
How do you know if someone has been inside your network for months? The answer lies in observability. In a region where regulatory frameworks are tightening—from Puerto Rico's data protection amendments to Brazil's LGPD influences—centralized visibility is not optional.
Elastic Security functions as the brain of the operation. By unifying logs, metrics, and traces from your entire infrastructure—endpoints, cloud workloads, network devices, and applications—Elastic enables your security team to detect anomalies in milliseconds rather than months.
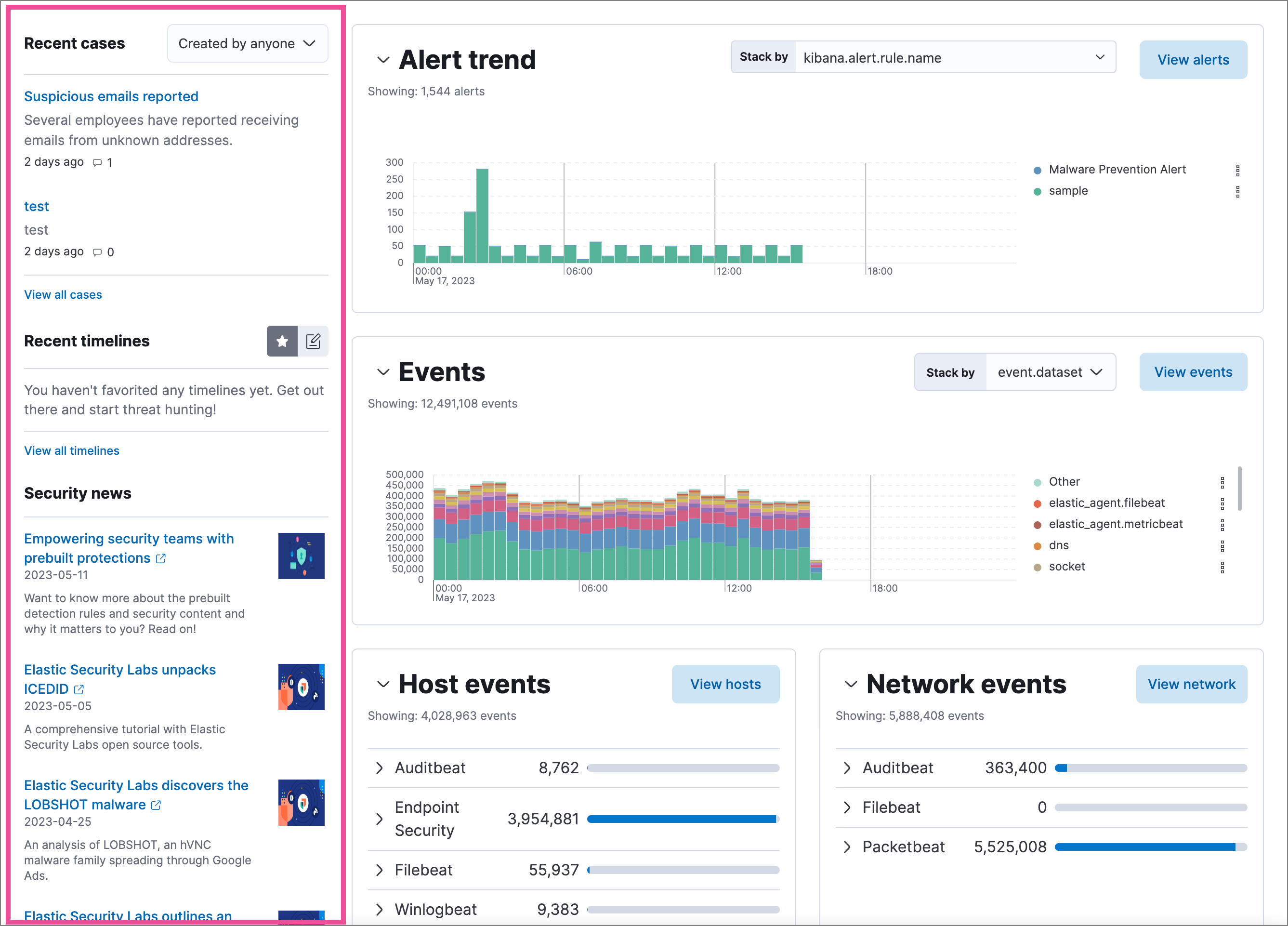
Why Elastic is ideal for LATAM enterprises:
- Open, Scalable Architecture: Avoids vendor lock-in and adapts to hybrid environments where on-premise legacy systems coexist with cloud-native applications.
- Prebuilt Detection Rules: Elastic provides out-of-the-box detection for threats commonly seen in financial services, including insider threat patterns and lateral movement techniques.
- Compliance Reporting: Generates audit-ready reports for regulators, mapping security events to frameworks like PCI-DSS, ISO 27001, and regional banking regulations.
At V-Corp, we leverage Elastic as the foundation of our Managed Detection and Response (MDR) offerings, giving mid-sized enterprises access to enterprise-grade SOC capabilities without the enterprise-grade headcount.
Layer 5: The Insurance Policy — Resilience with Veeam
The question is no longer if you will be attacked, but when. And when that moment arrives—whether through ransomware, insider sabotage, or a Category 5 hurricane making landfall—your ability to recover determines whether you survive as a business.
Veeam Data Platform provides the architectural certainty that your data is protected, immutable, and recoverable. Their modernized 3-2-1-1-0 backup rule is the most affordable insurance policy any CIO can implement:
Breaking down the rule for Caribbean resilience:
- 3 copies of your data
- 2 different media types
- 1 copy offsite (critical: for the Caribbean, this means geographically outside the hurricane belt)
- 1 copy offline, air-gapped, or immutable
- 0 errors after recovery verification
Veeam's immutability features are particularly relevant in 2026. Modern ransomware actively seeks and destroys backups before encrypting production data. Veeam's hardened Linux repository and object-lock capabilities ensure that even if attackers gain domain-administrator access, they cannot touch your last line of defense.
For organizations in the Caribbean, we architect Veeam replication targets in cloud regions outside the storm zone, ensuring that a hurricane in San Juan never becomes a data-loss event.
The V-Corp Integration: Why Ecosystems Beat Products
Each of the technologies above is best-in-class in its domain. But the magic—and the security—happens in the integration. At V-Corp International, we do not distribute hardware; we engineer ecosystems.
| Layer | Technology | V-Corp Value Add |
|---|---|---|
| Perimeter | Fortinet | Custom SD-WAN design for multi-island latency optimization |
| Barracuda | BEC playbooks tailored to regional business culture | |
| Application | F5 | API discovery and PCI-DSS compliance mapping |
| Observability | Elastic | 24/7 MDR with Spanish/Portuguese-speaking analysts |
| Resilience | Veeam | Hurricane-resistant off-island replication architecture |
This is the difference between buying security tools and building digital sovereignty. When your Fortinet fabric detects a threat, Elastic correlates it, F5 blocks lateral movement at the app layer, Barracuda prevents email-based propagation, and Veeam ensures you can rebuild if everything else fails.
The Time for Reactive Security Is Over
Latin America and the Caribbean are not emerging markets for cybercriminals—they are priority targets. The institutions that thrive in 2026 and beyond will be those that stopped thinking of security as a cost center and started treating it as competitive infrastructure.
Your company's digital sovereignty depends on the quality of its allies. At V-Corp International, we bring together the world's leading security technologies with deep regional expertise in the Caribbean, Central America, and South America. We understand the regulatory landscape, the climatic realities, and the operational constraints because we operate where you operate.
Take the Next Step
Don't wait for the next security breach report to justify your investment.
👉 Explore our regional inventory and solutions — Discover how Fortinet, F5, Elastic, Barracuda, and Veeam can be integrated into your environment.
👉 Book a complimentary security architecture consultation — Our engineers will assess your current posture and design a layered defense strategy tailored to your industry, whether you operate in offshore banking, hospitality, retail, or critical infrastructure.